Update of a leak: Bad QA of iOS 15.0.2 led to comprehensive exposure of ISO.org
Update 26.10.2021:
After additional investigation of initial exposure of ISO.org Content Server, we finally concluded that exposed information is not for public access.
For the time of investigation, we can search through very convenient internal search queries and observe:
- 490k+ different documents
- 120k+ emails
- 5k+ different media files
By the way, look at the dates below. It seems that with COVID-19 and lockdowns, all internal and external events were postponed or canceled, so there are almost no photos after November 2020.

We were in contact with the hacker, who discovered this leak and received proof of him contacting both parties involved in the story but without any response or reaction.
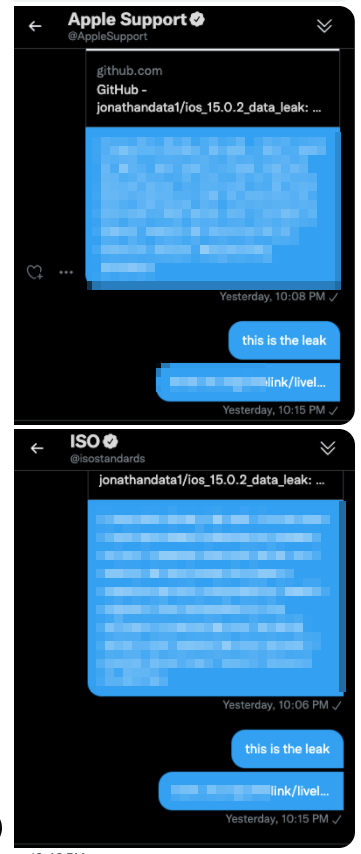
We tried to communicate ISO.org too, but with the same zero results.
We can also confirm the exposure of private data of ISO.org members through unprotected Content Server, which was under question.
One may see on the screenshot, the data sample is limited to 10000 results for a query, but nobody limits the number of queries; thus, there can be much more PII data stored.

As Jonathan Scott has revealed 10/21/2021 in his GitHub repository, Apple iOS developers made a crucial mistake that led to a major data exposure in ISO.org

Image source – twitter.com
Code exposes backdoor that bypasses a paywall
A bad review of code in iOS 15.0.2 led to the exposure of the something being public repository of the ISO.org.

Image source – github.com
Jumping around the pages on the provided link, one can find a lot of interesting documents.

But at the end, it is all public data, while any links to private areas are not accessible without proper authentication.
It is yet unclear if there are any paid documents and developing standards leaked.
Exposure of PII is not just a standard for free
As a sample, you can see the 10k records with usernames, first names, last names, and email addresses from all around the world. This data is associated with many governmental and international organizations.

Image source – github.com
About the Hacker
According to self-provided information, Jonathan Scott is one of the top hackers in the United States regarding hacking ethics.
His profile on HackerOne is still existing, but didn’t filled with any kind of data.
I was the #1 hacker in the USA for the last 90 days on Hackerone.com, and I was kicked out for speaking up about a data leak that was ignored, but yet fixed behind my back
Jonathan Scott
Ethical issue
Since data provided by the hacker is valid and the mentioned service of ISO.org is still available, there are questions about ethical side of such disclosure remaining open.
The Cooltechzone explicitly discourage non-ethical disclosure of security issues. We are sure there is no data leak in this particular case.
The information provided here is only to raise awareness and not intended to provide any support to anybody for exploitation of vulnerable resources.
Comments
You should update this article to point out his antics clearly, as he is now using this very article to legitimize his fraudulent research.
But more important, it is putting under attack any third-parties, which are in their order can be 2 tier delivery for other products.
Your email address will not be published. Required fields are marked