We have written malicious chrome extension and check how it is dangerous for users

As investigated by the Security firm Awake, Above 100 malicious Google Chrome browser extensions gathered 33 million downloads.
Not only that, these 111 malicious extensions were found to spread spyware in the millions of devices they were downloaded.
The Awake report made clear that malicious extensions installed the Chromium open-source version of Chrome which made running without Google's approval possible. They also never appeared in the Chrome Web Store.
The malicious actors need to be dealt with by being aware of their tactics.
Without further ado, let's dive right into it!
Table of Contents
- Why is Chrome dangerous?
- What are Chrome Extensions & how do they work?
- Creating & Publishing the Chrome Extension
- Malicious Chrome Extensions
- How do I know if the extension is Malicious?
- How Chrome Extensions can be dangerous for users?
- Sabre-Security Architecture for Browser Extensions
- How to get rid of malware tools?
- Conclusion
Why is Chrome dangerous?
Chrome as a popular browser has a long history with vulnerabilities.
We can track it thanks to cvedetails. As one might seen, there is not unusual peaks of discoveries along the timeline – there is quite stable discoveries rate.

Image source – cvedetails.com
Few last dangerous vulnerabilities were announced recently by Kaspersky. They are having CVSS 7-8 points and exploit incorrect use of heap memory, that potentially leads to arbitrary code execution on the targeted computer – simply, taking over the target.
What are Chrome Extensions & how do they work?
If we talk about what the Chrome Extensions are, we get the idea that they are nothing more than minor plans that customize the browsing experience. They are built on web pages of JavaScript, HTML, and CSS.
Extensions let you expand the program by utilizing APIs to alter program conduct and access web content. Extensions work through an end-client UI and a designer API.
They are more than the 137,345 Chrome Extensions that can easily be installed from Chrome Web Store.
Some of the most valuable extensions counted in Chrome are AdBlocker Ultimate, The Great Suspender, and Flow Crypt.
Creating & Publishing the Chrome Extension
- Before You Begin, Make Strategy in Mind
- Setting Up Things for Chrome Extension
- Test Your Extension
- Making things nicer
- Deploy it on Chrome Web Store
Using the different development tools, we create extensions that help users by providing many services like Productivity tools, Web page content enrichment, and Information aggregation.
Most Chrome consumers get extensions from the Chrome Web Store. Designers across the globe distribute their augmentations in the Chrome Web Store, where they are checked on and made reachable for end clients.
We will now create a web extension for Chrome.
Before You Begin, Make Strategy in Mind
Before starting to build anything, make a rough idea in your mind or jot the points you are up to and which type of consumers will be helpful.
It doesn't need to be some new innovative idea. It can be the same as some previous extensions in use. Still, they might need some reshaping in structure and managerial things.
So, before you get to create an extension, you must start with some plan in mind.
Setting Up Things for Chrome Extension
Being a developer, you can build an extension. These steps that you must follow are:
- Create a folder naming the same as the app or extension name
- The first step is to create a manifest file named manifest.json. It's a metadata document file in JSON design that contains properties like your expansion's name, depiction, variant number, etc. In this record, we mention to Chrome what the augmentation will do and what consents it requires
- Make sure that JSON code is formatted correctly with a third-party JSON tool
- Specify the icon for your extension

You must be thinking about what kind of permission must be adopted. It depends on the extension you are supposed to do.
["activeTab", "declarative content", "storage", "
In the above example, we need such information about the active tab, changes the page content, access local Storage, and be active on all sites.
Test Your Extension
Now it's time to check if your extension works on Chrome and meets the expectations as it was desired to be. For testing the extension, follow these steps:
- Go to Chrome Extension in Chrome Browser
- Check Developer Mode in the top right-hand corner

- Select Load Unpacked to see the file section dialogue box

- Select the extension directory that you created.
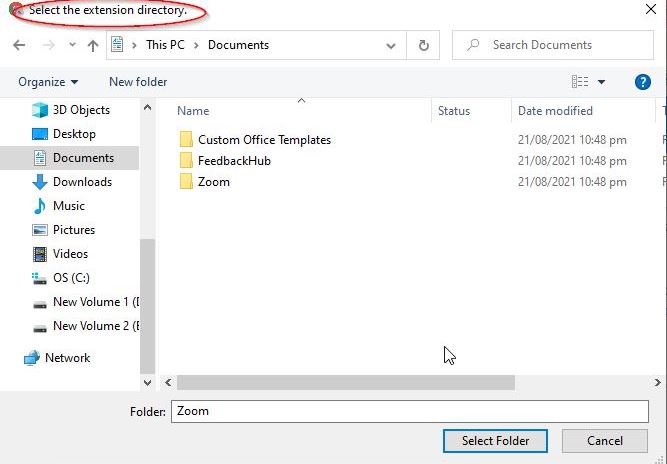
If your extension works, it will load immediately. Otherwise, you will see an error message at the top of the page. Try to correct those errors to make the extension works specifically.
After that, you need to add a background script that tells your extension what to perform. Add it to your specified folder after creating the specified js file for the background generator to work.
This file will open aware Chrome that it needs to scan for additional instructions. The extension we are building will also require a listening event for runtime.on installed within the background script.
Making Things Nicer
After ensuring that everything works nicely no need to make it more excellent. Create the CSS file in a specified folder of extension. Write code for a CSS file that makes it look impressive, then link it into your HTML or JSON file by providing links to the CSS file.
The equivalent goes while including a JavaScript document for any dynamic usefulness that you might want to incorporate. Known that you have made a website page previously, you would now be able to utilize your sorcery to show your clients anything you desire.
Deploy It on Chrome Web Store
Once you are done with everything, like making it work properly, making it more excellent, and combining all the files, it's time to publish it to Chrome Store. You will be asked to sign in to google if you are not signed in.
Then click the Add new item button, accept terms and conditions, and you will get to a page where you can upload your extension.

Malicious Chrome Extensions
According to a recent study, malicious extensions redirect users to ads or unusual sites that collect browsing history, personal data like birth dates, email addresses, active devices, and even download further malware onto a device.
These extensions are made by hiding some dangerous code in making chrome extensions of which the user is unaware, and he adds those extensions, and this work is illegal.
On checking the malicious chrome extensions, it was found that they contain jumbled JavaScript code.
SHA1 hashes contained by these malicious files are:
- 027a7f5474168be5e8f8cba16bee3703c5b7e2ee
- b7d2c9d221e0e04ffb8090d3067c9b8ee50967e0
How do I know if the extension is Malicious?
Open extensions by clicking on the icon in the top right corner of your browser, then tap the three dots and select Manage extensions.

Once the new tab opens, if you examine the URL, you'll see something that looks like chrome://extensions/?id=oiigbmnaadbkfbmpbfijlflahbdbdgdf.

The highlighted gibberish is an extension ID of 32-characters.
On Comparing the extensions' IDs of your installed extensions, if any one of them matches the ones given below, remove the extension.
These extension IDs given below are found to be malicious:
- acmnokigkgihogfbeooklgemindnbine
- apgohnlmnmkblgfplgnlmkjcpocgfomp
- apjnadhmhgdobcdanndaphcpmnjbnfng
- blngdeeenccpfjbkolalandfmiinhkak
- ccdfhjebekpopcelcfkpgagbehppkadi
- cceejgojinihpakmciijfdgafhpchigo
- cebjhmljaodmgmcaecenghhikkjdfabo
- chbpnonhcgdbcpicacolalkgjlcjkbbd
- cifafogcmckphmnbeipgkpfbjphmajbc
- clopbiaijcfolfmjebjinippgmdkkppj
- cpgoblgcfemdmaolmfhpoifikehgbjbf
- dcmjopnlojhkngkmagminjbiahokmfig
- deiiiklocnibjflinkfmefpofgcfhdga
- dipecofobdcjnpffbkmfkdbfmjfjfgmn
- dopkmmcoegcjggfanajnindneifffpck
- bannaglhmenocdjcmlkhkcciioaepfpj
- bgffinjklipdhacmidehoncomokcmjmh
- bifdhahddjbdbjmiekcnmeiffabcfjgh
- bjpknhldlbknoidifkjnnkpginjgkgnm
- dopmojabcdlfbnppmjeaajclohofnbol
- edcepmkpdojmciieeijebkodahjfliif
- ekbecnhekcpbfgdchfjcfmnocdfpcanj
- elflophcopcglipligoibfejllmndhmp
- eogfeijdemimhpfhlpjoifeckijeejkc
- bahkljhhdeciiaodlkppoonappfnheoi
- fcobokliblbalmjmahdebcdalglnieii
- fgafnjobnempajahhgebbbpkpegcdlbf
How Chrome Extensions can be dangerous for users?
Google Chrome extensions can increase the browser's usefulness, but some wrong actions might harm the users.
Malicious Domain Registrars
According to an investigation, it's revealed that an enormous worldwide surveillance mission is influencing a great many users.
The mission included many domains and malicious Chrome extensions, with all the movement tying back to a single internet domain registrar.
Format as a citation:
These malicious Chrome extensions performed tasks such as taking screenshots of the victim's device, reading the clipboard, loading malware, and actively harvesting tokens and user input. Google has brought down these extensions following Awake's disclosure.
However, this mission could keep away from discovery by state-of-the-art security tools through several evasion plans. Malicious Domain Request 22 is a notification that can be found on the Norton Antivirus extension.
Stealing Sensitive and Private Data
Chrome and other browser extensions represent a precious strategy for attackers since host-based security arrangements will generally experience authentic information from malicious activity performed inside the browser.
It is particularly problematic since many people conduct a critical piece of their day-by-day business activities inside the browser.
From the appearance, the sleeper agent extensions seem to be idle.
We accept these are important for a broader pattern where malicious actors push malicious payloads to browser apps and extensions after the "clean" version has been approved.
It's meager for a malicious actor to get the extension published and dynamically change the behavior later on after it's published.
Jake Williams, a Rendition Infosec
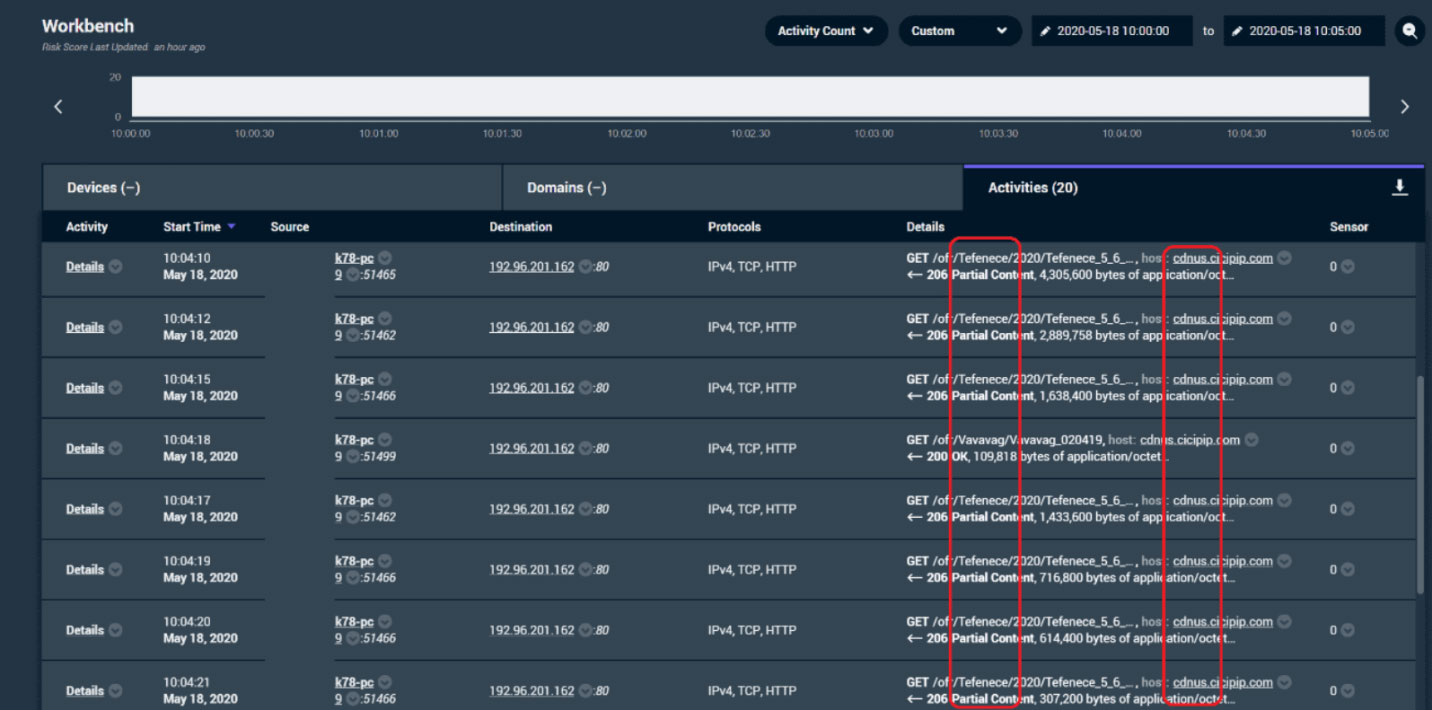
Image source −cybersecuritynews.com

Image source – cybersecuritynews.com
Spyware
A newfound spyware exertion assaulted clients through 32 million downloads of extensions to Google's market-driving Chrome web browser.
Most free extensions are suspected to caution users about sketchy sites or convert documents starting with one organization then onto the next.
All things being equal, they redirected browsing history and information that gave credentials for access to internal business tools. Considering the number of downloads, it was the broadest malicious Chrome store mission to date.
These extensions were able to bypass identification (sandboxes, response solution, web proxies, and endpoint detection) by antivirus organizations or security programming that asses the reputation of web domains through an infrastructure of 15,160 malicious or suspicious domains.
A malicious Chrome extension might also be employed as an attack vector in XSS injections. A malicious script is usually fused into otherwise safe websites, called as Cross-Site Scripting attacks.
If somebody used the browser to surf the web on a home PC, it would associate with a progression of sites and communicate data, the analysts found. Most of the VPNs in chrome extensions that can be installed free can work as spyware.
Malware
Chrome extensions may be hiding malware or contained code to bypass Google's Chrome
Web Store security scans, even when you install them from the official Chrome Web Store. The extensions took on the appearance of standard utilities, with names like "Stickies" and "Lite Bookmarks".
However, the analysts saw signs that they were pretty part of click-fraud scams to boost revenue for attackers. Google eliminated the four augmentations after Icebrg revealed them privately.
And the more frameworks and services move into the browser—like Google's G Suite—the more significant data and network access a malicious Chrome extension might get.
As well as circulating malware through components like phishing and compromised locales, attackers have likewise refined procedures to pirate their extensions into the Chrome Web Store. Afterward, they modify them distantly once downloaded to add or initiate awful elements.
SABRE-Security Architecture for Browser Extensions
Dhawan, Mohan & Ganapathy, Vinod from the Department of Computer Science in The State University of New Jersey, proposed a solution for malicious chrome extensions in their research "Analyzing Information Flow in JavaScript-Based Browser Extensions".

Image source − slideplayer.com
We endorse Sabre (Security Architecture for Browser Extensions), which analyzes JSEs.through in-browser-information flow tracking.
Malicious JSEs can abuse the privileges to compromise security by stealing confidential information through stored passwords and cookies or by executing random code in a web application.
Even if JSE is not malicious, vulnerabilities in JSE and the browser could allow a remote attacker to compromise browser security.
Sabre determines if the object contains sensitive information by associating a tag with every JavaScript object in the browser memory. Unlike JavaScript code in a web application, code in JSE is not constrained by its policy.
Sabre alerts when objects are modified by JSE and propagated between browser subsystems. Saber generates a warning if an object containing confidential information is accessed insecurely, for example, if JSE tries to write it to a file or send an object over the network.
We implemented Sabre by modifying the Firefox browser and testing it using malicious and secure JSEs containing exploitable vulnerabilities. Our tests show that Sabre can pinpoint potential disruptions to JSE information flows.
How to get rid of malware tools?
I've put together a few simple guidelines for you to help you get rid of potentially dangerous browser extensions:
- Ensure the developer of the extension is legitimate.
- Just install extensions from official web stores like the Chrome Web Store.
- Go through all the permissions that an extension demands carefully.
- Try not to install a boatload of extensions.
- Regularly go through installed extensions and make sure they're still working usually.
- Make sure to have security software installed.
- Use security browsers as an alternative to Google Chrome
Conclusion
Today you learned that third-party utilities could be as dangerous as the Chrome browser itself.
We may not even guess that the extension we installed is a real spy tracking our actions! Hope my research can help improve your internet security.
What else do you want me to write on? Let me know in the comments! I look forward to your questions and suggestions.
Stay safe!
Your email address will not be published. Required fields are marked